OAuth 2.0
Requesto has built-in OAuth 2.0 support with automatic token management.
Supported Grant Types
- Authorization Code - standard server-side flow
- Authorization Code with PKCE - PKCE challenge/verifier generated automatically
- Implicit - browser-based (deprecated in OAuth 2.1)
- Client Credentials - server-to-server, no user involved
- Resource Owner Password - direct username/password exchange
Creating a Configuration
- Go to the OAuth 2.0 page
- Click New Configuration
- Fill in the fields for your chosen grant type
- Click Save
Common fields:
| Field | Description |
|---|---|
| Client ID | From your OAuth provider |
| Client Secret | From your OAuth provider (stored server-side only) |
| Authorization URL | Provider's authorize endpoint |
| Token URL | Provider's token endpoint |
| Redirect URI | Auto-detected from your browser URL - typically http://localhost:5173/oauth/callback in dev or http://localhost:4747/oauth/callback in Docker |
| Scopes | Space-separated list of permissions |
Authorizing
- Click Authorize on your config
- A browser window opens to the provider's login page
- After granting access, the provider redirects back to Requesto
- The access token is stored client-side
Using a Token in Requests
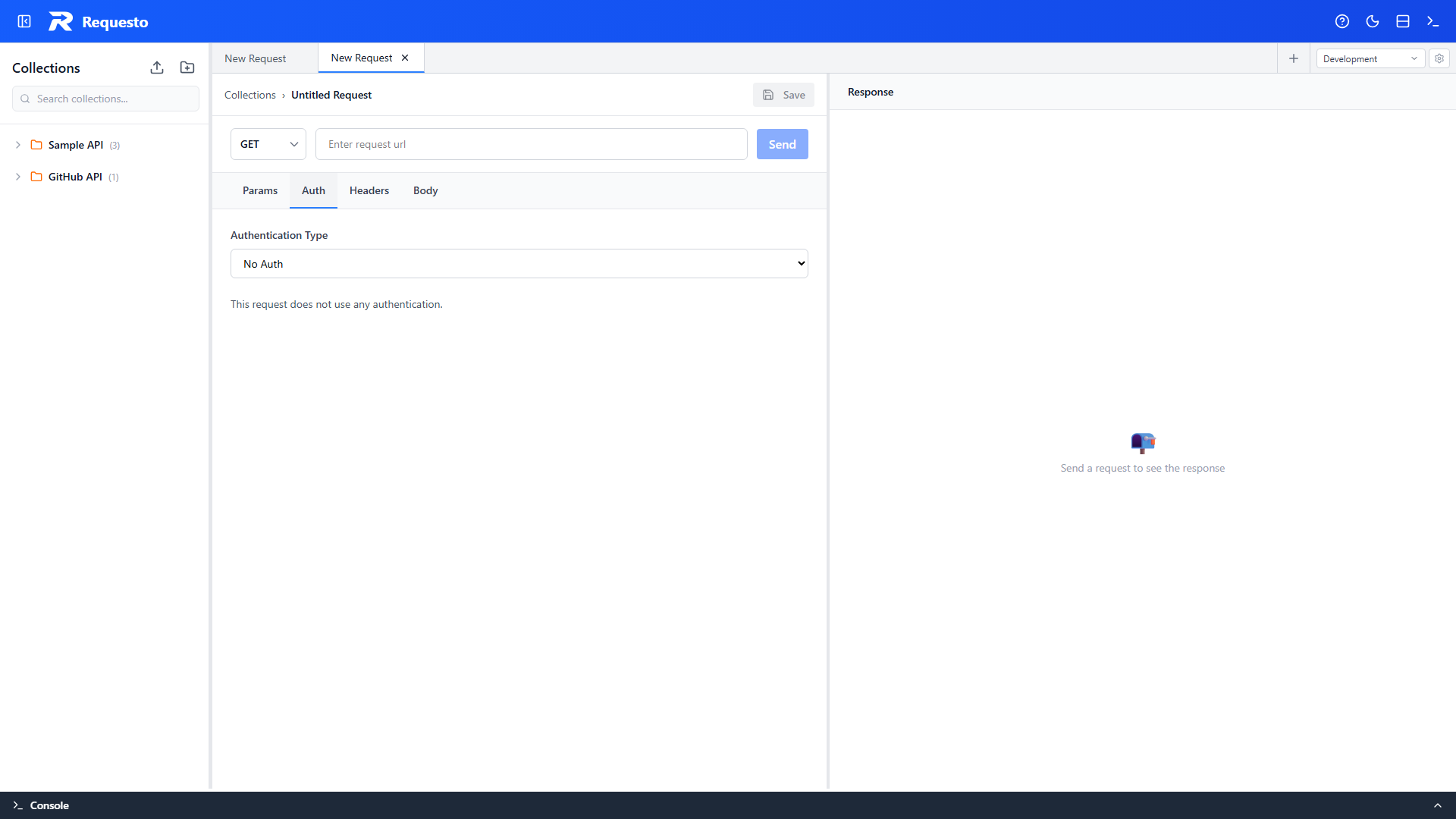
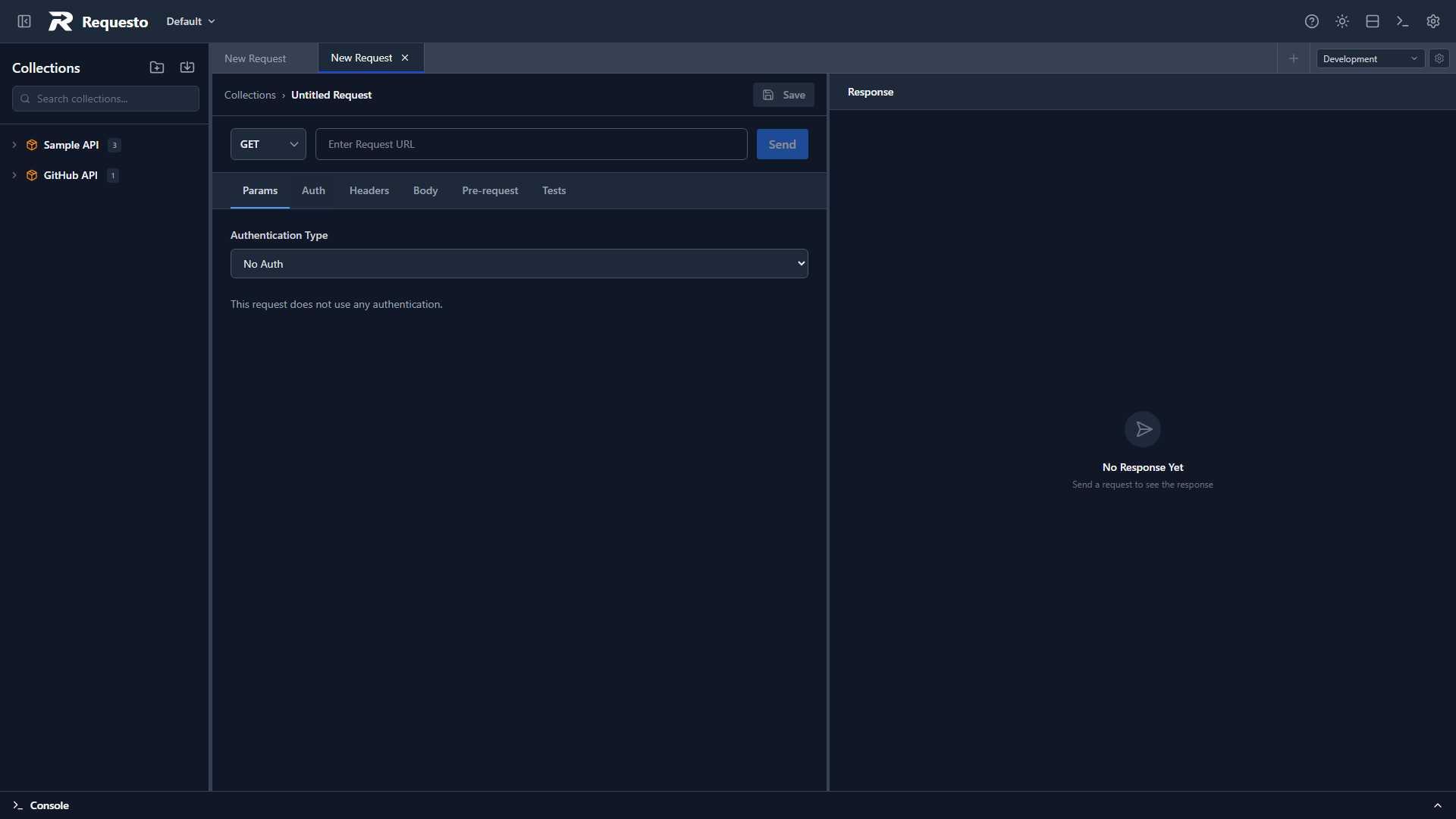
In a request's Auth tab:
- Select OAuth 2.0 as the auth type
- Pick your saved configuration
- Send the request - the token is added as
Authorization: Bearer <token>
Token Storage
- Access tokens and refresh tokens: stored client-side (sessionStorage or localStorage, depending on your config choice)
- Client secrets: stored server-side only in
oauth-configs.json- never exposed to the frontend
Choose Session storage if tokens should be cleared when the browser tab closes, or Persistent if you want them to survive across sessions.
Automatic Refresh
If Auto Refresh Tokens is enabled on a config:
- Requesto will automatically refresh the token before it expires
- The refresh threshold (seconds before expiry) is configurable per config
You can also manually refresh by clicking Refresh Token on the OAuth page.
PKCE
When using the Authorization Code with PKCE grant type, PKCE is handled automatically - a code verifier and SHA-256 code challenge are generated with no extra configuration.
A state parameter is also generated automatically for CSRF protection on all authorization code flows.
Provider Examples
GitHub
Grant Type: Authorization Code
Authorization URL: https://github.com/login/oauth/authorize
Token URL: https://github.com/login/oauth/access_token
Scope: user repoGoogle
Grant Type: Authorization Code with PKCE
Authorization URL: https://accounts.google.com/o/oauth2/v2/auth
Token URL: https://oauth2.googleapis.com/token
Scope: openid https://www.googleapis.com/auth/userinfo.emailSpotify
Grant Type: Authorization Code with PKCE
Authorization URL: https://accounts.spotify.com/authorize
Token URL: https://accounts.spotify.com/api/token
Scope: user-read-private user-read-emailTroubleshooting
"Invalid Redirect URI" - The redirect URI registered with your provider must exactly match what Requesto sends. Check the auto-detected URI shown in the config form and register that exact value with your provider.
Token not refreshing - Make sure Auto Refresh is enabled in the config, and that your provider actually issued a refresh token (not all do).
Authorization window not opening - Check that your browser isn't blocking the popup. Verify the authorization URL is correct.
Self-signed certificate on the token endpoint - If your OAuth provider's token URL uses a self-signed or otherwise untrusted TLS certificate, enable Ignore SSL certificate errors in Settings. This applies to both OAuth token exchange and outgoing API requests.